Compliance Management
Trusted by growing Australian businesses
- 150+ companies served
- 20+ industries
- 48 5-star reviews
- 100% Australia-based team

Understand Your Compliance Gaps
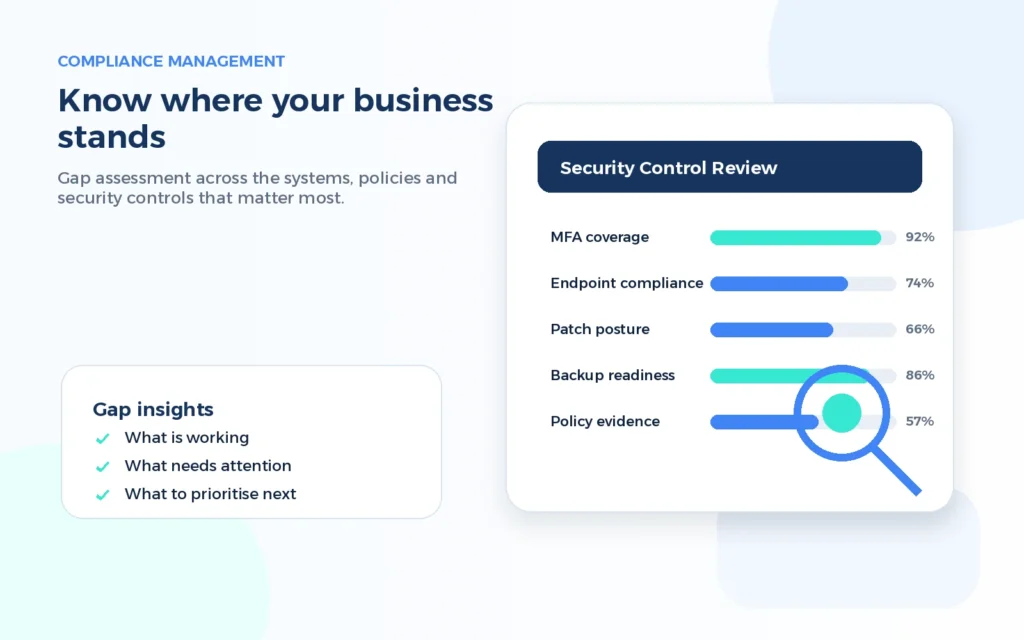
Security compliance is much easier to manage when you know exactly where your business stands. Stanfield IT reviews your current systems, processes, documentation and security controls to identify what is working well and what needs attention.
This may include reviewing Microsoft 365, identity security, device management, backups, patching, access controls, policies and existing evidence. We look at the practical areas that affect your ability to meet client, insurance, governance or framework requirements.
The result is a clear view of your current position. Instead of guessing what needs to be fixed, your business gets a structured summary of gaps, risks and priorities. This helps leadership make informed decisions and gives your team a sensible starting point for improvement.
Create a Clear Remediation Plan
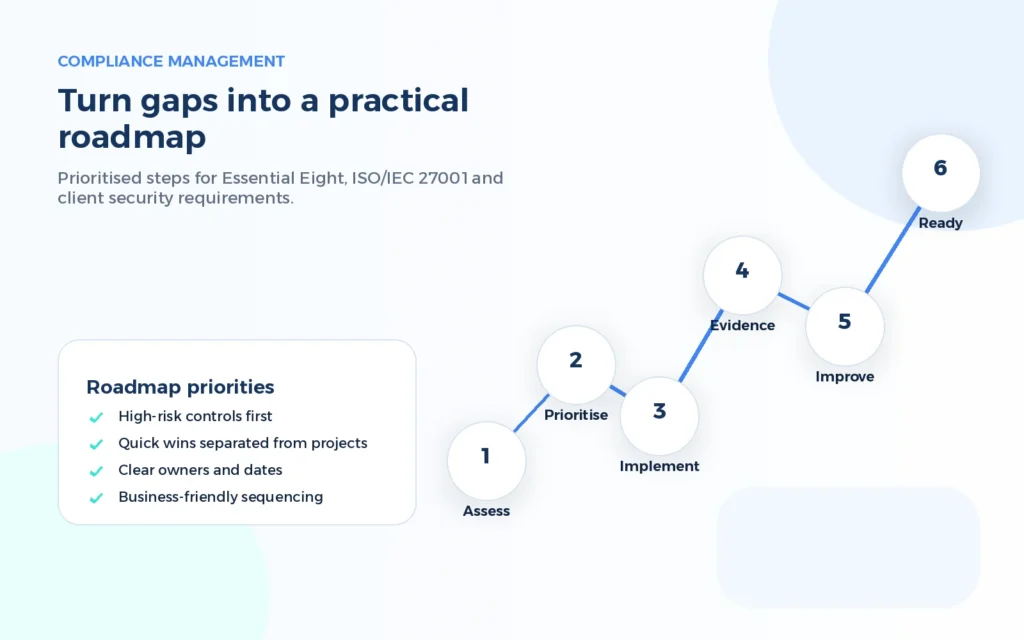
A long list of compliance findings can feel overwhelming. Stanfield IT turns assessment results into a practical remediation plan that separates urgent risks from longer-term improvements.
Your roadmap can be aligned with the Essential Eight, ISO/IEC 27001 readiness, cyber insurance requirements, client contract obligations or internal governance goals. Each recommendation is explained in plain English so business owners, operations teams and technical staff can understand the purpose behind the work.
We help define what should happen first, what can be planned for later and which changes will deliver the most value. This makes compliance management easier to approve, budget and track over time.

Implement Practical Security Controls
Compliance becomes valuable when recommendations are converted into working security controls. Stanfield IT can help implement and manage practical improvements across identity, devices, email, cloud platforms, backups, user access and reporting.
This may include multi-factor authentication, Conditional Access, endpoint management, patching processes, administrator access controls, backup monitoring, policy updates and security awareness activities.
Because Stanfield IT works across IT support, cloud services and cyber security, we understand how to make improvements without unnecessarily slowing your team down. The goal is to strengthen your security posture while keeping everyday business operations running smoothly.
Compliance Management
Gap Assessment
Get a clear understanding of your current compliance position. Stanfield IT reviews your systems, controls and documentation to highlight risks, missing evidence and practical areas for improvement.
Essential Eight Support
Stanfield IT can help assess, prioritise and improve controls aligned to the Essential Eight, giving your business a clearer path towards stronger cyber security maturity.
ISO 27001 Readiness
Prepare for ISO/IEC 27001 with support across control reviews, documentation, evidence organisation and practical security improvements that suit your business environment.
Evidence Management
Keep compliance evidence organised and easier to access for audits, client reviews, insurance renewals and leadership reporting. This reduces last-minute stress and improves visibility.
Risk Tracking
Track identified risks, assigned actions and remediation progress in a structured way. This helps decision-makers understand what has been completed and what still needs attention.
Ongoing Governance
Compliance is not a one-time activity. Stanfield IT can support ongoing reviews, reporting, roadmap updates and control checks as your business systems and risks change.

Keep Evidence and Reporting Ready
Many businesses have security controls in place but struggle to prove it when a client, insurer or auditor asks for evidence. Compliance management helps bring that information together so reporting becomes easier and more reliable.
Stanfield IT can help maintain control registers, risk registers, remediation trackers, policy evidence, reporting packs and review notes. This gives leadership a clearer view of progress and helps your team understand what has been completed, what is still open and why each action matters.
Better reporting also helps compliance stay active. Instead of waiting until an audit deadline, your business can review its position regularly and keep security improvements moving.
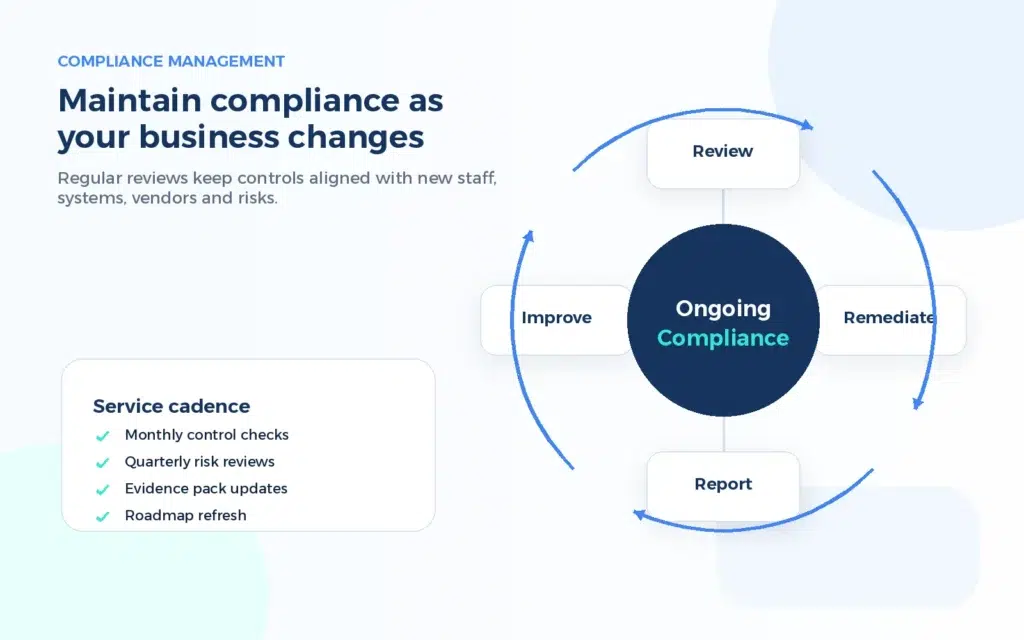
Review Compliance as Business Grows
Your compliance position can change as your business adds staff, devices, cloud services, vendors and new ways of working. Controls that were suitable last year may need to be reviewed as your environment changes.
Stanfield IT helps keep compliance management active through regular reviews, evidence updates, roadmap refreshes and practical guidance. This reduces the chance of gaps reappearing and helps your business stay ready for client security reviews, cyber insurance requests and internal governance discussions.
The aim is simple: make compliance easier to maintain, reduce avoidable risk and give your business a stronger security foundation as it grows.
Who our Compliance Management Services are for
Growing SMEs
Small and medium businesses that rely on technology, cloud platforms and client data can use compliance management to improve security without needing a full internal governance team.
Client-Facing Firms
Businesses responding to client security questionnaires, tender requirements or contract reviews can benefit from clearer evidence, stronger controls and more organised reporting.
Cyber Insurance Needs
Organisations preparing for cyber insurance renewals or security reviews can use compliance management to identify gaps and demonstrate practical progress.
Lean Internal IT Teams
Internal IT teams with limited time can use Stanfield IT for assessments, prioritisation, remediation support and ongoing compliance tracking.
Trusted Compliance Support
- Clear advice without unnecessary complexity
- Practical support across IT, cloud and cyber security
- Reporting that helps leadership understand risk
- Ongoing reviews to keep compliance moving
Frequently Asked Questions
-
Compliance management is the process of assessing, improving and maintaining security controls, documentation, reporting and evidence for business, client or framework requirements.
-
Yes. Stanfield IT can assess your current position, identify gaps, prioritise remediation and support practical improvements aligned to the Essential Eight.
-
Stanfield IT can support ISO/IEC 27001 readiness through control reviews, documentation support, evidence organisation and security improvement planning.
-
Not always. Some businesses need certification, while others need better governance, insurance readiness or client assurance. We help you choose the right level of structure.
-
Timing depends on your systems, documentation and requirements. A focused review can usually be completed first, followed by a prioritised roadmap for improvement.
-
Stanfield IT plans changes carefully and aims to reduce disruption. We focus on practical improvements that strengthen security while supporting normal business operations.
Simplify Compliance
Book a review and get a clear plan for your next compliance priorities.
