Patient data is the lifeblood of many healthcare organisations. It houses critical information like medical histories, Medicare identifiers, and payment details. However, the industry has seen a surge in cyber security threats. The current threat environment underscores the absolute necessity for a robust approach to cyber security within the healthcare sector. This isn’t just to protect sensitive patient information from hackers, but also to maintain the trust and confidence of those who entrust healthcare providers with their most personal details.
In this blog, we’ll dive into the importance of cyber security in the healthcare sector and provide an overview of patient data protection. We’ll also discuss common cyber security threats faced by healthcare organisations and preventive measures that can be taken to avoid breaches.
Additionally, we’ll explore regulations and compliance in healthcare, as well as best practices for implementing cyber security solutions. Read on to learn about the steps you can take to protect your patients’ information and ensure their trust in your organisation.
Get Your Free Essential Eight Cyber Security Report
Learn:
-
- The cyber security gaps costing you time and money.
- Practical steps to upgrade your security measures.
- The hidden risks of poor security protocols.
- How to bolster your cyber security and aid business growth.
What is Cyber Security for Healthcare?
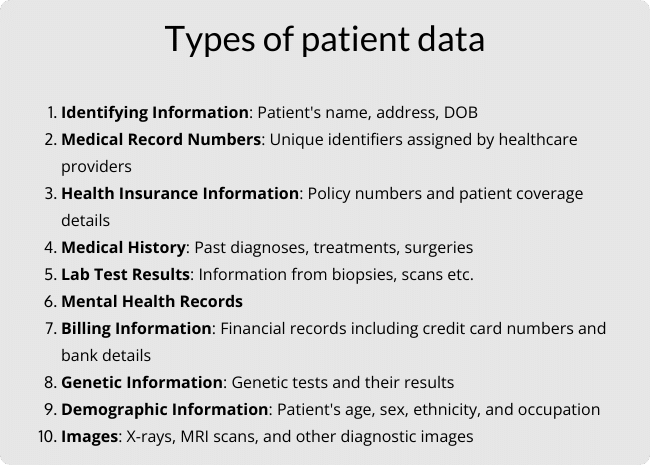
Cyber security for healthcare refers to the collective methods, processes, and practices designed to protect networks, devices, programs, and data from digital attacks, damage, or unauthorised access within a healthcare setting. These practices are vital in protecting against cyberattacks that could impact:
- Sensitive patient information
- Hospital records
- Communication infrastructure
With the growing dependence on electronic health records (EHRs), telemedicine, and connected medical equipment, the importance of cyber security has increased dramatically. It’s crucial to protect these systems from cyber threats such as malware, ransomware, and phishing emails.
Lastly, effective cyber security in healthcare isn’t just about technology. It involves creating a culture of security aware people. This includes everyone from the reception desk to the doctor’s office. Training and awareness programs ensure the human element strengthens, rather than weakens, the security chain.
Overview of Patient Data Protection
Securing patient data is at the core of healthcare cyber security. Given the rise of sophisticated ransomware attacks and diverse cyber threats, the defence of sensitive patient data is mandatory.
Compliance with regulations such as HIPAA and the Privacy Act is just the starting point. Healthcare providers must go above and beyond adopting industry best practices for information security. This includes fortifying electronic health records (EHRs) and medical devices with measures like multi-factor authentication and conducting regular cyber security training for employees. All this serves not only to prevent damaging data breaches but also to enhance patient care and outcomes.
Importance of Cyber Security in the Healthcare Sector
There are a few reasons why cyber security is so important in healthcare. For starters, the healthcare sector is a prime target for cybercriminals due to the sensitive and valuable patient data it holds.
In fact, healthcare is typically one of the hardest hit industries when it comes to cyber crime. See below to see how it compares to other Australian industries.
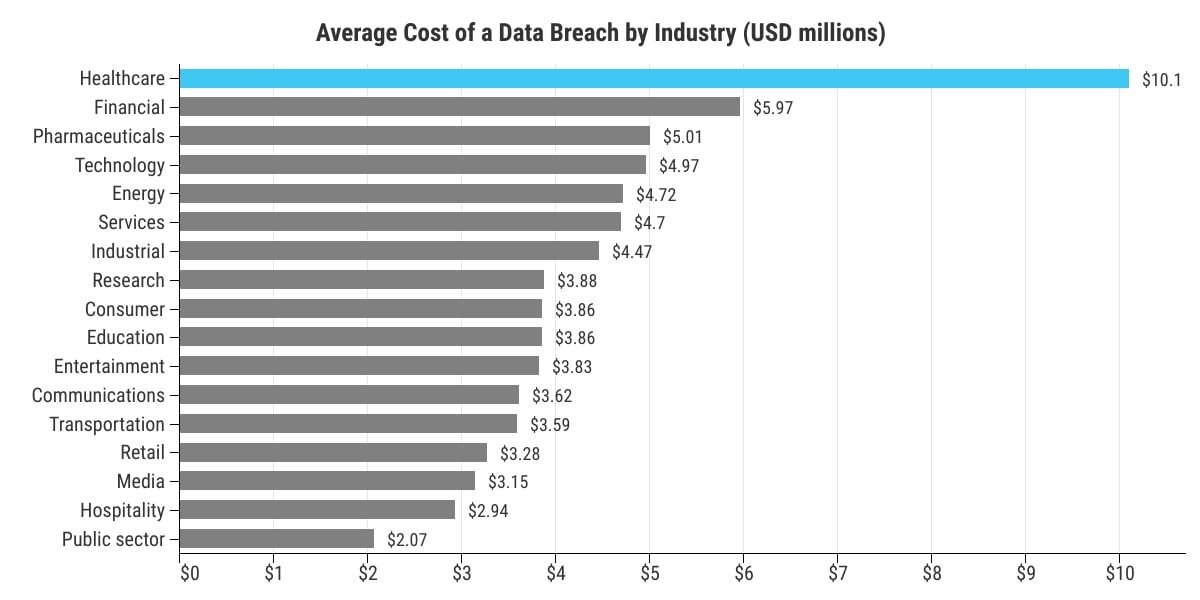
As you can see security breaches can result in serious financial loss. However, that’s not all, other serious consequences include damage to reputation and compromised patient privacy.
To prevent such incidents from occurring in the first place, effective cyber security measures such as encryption protocols, access controls management systems and employee training programs are necessary.
Role of Stakeholders in Cyber Security
When it comes to upholding cyber security in healthcare, it’s all hands on deck.
Various stakeholders in healthcare have key roles. For instance, healthcare providers are responsible for implementing strong security safeguards and abiding by regulations to keep patient data secure.
But, let’s not forget our tech gurus – the IT pros. Their job is to set up secure networks and keep software updated to ward off any cyber attacks.
Everyone has a part to play. And when we join forces, we’re better equipped to keep the healthcare sector protected from malicious actors.
Understanding Cyber Security Threats in Healthcare
Healthcare facilities are prime targets for criminals due to the value of health information. To safeguard patient data and ensure continuity of care, healthcare providers must adopt best practices to secure their information technology infrastructure.
Things like multi-factor authentication, consistent staff training, and having a cyber security response plan are key to fending off ransomware strikes and data breaches. Additionally, measures to secure medical devices and EHRs are key.
By establishing a robust governance system, healthcare organisations can protect patient welfare and shield their institutional reputation from the damaging effects of cyber threats.
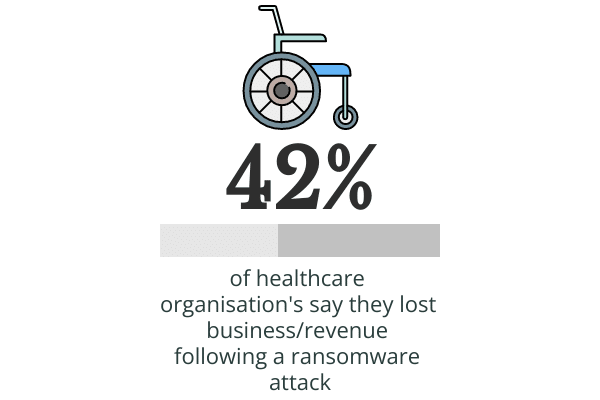
Ransomware Attacks in Healthcare
Ransomware attacks are a form of digital hostage taking – where attackers hold your data captive until a ransom is paid. The aftermath? Disruptions to patient care and threats to patient well-being.
For healthcare institutions, a strong IT framework and strict governance practices are essential.
One way to soften the blow of ransomware attacks and reduce downtime is to maintain regular backups of health records. The ultimate goal is to protect patient safety and ensure optimal care outcomes.
Common Cyber Security Vulnerabilities in Healthcare
Healthcare cyber security is constantly plagued by persistent threats that put the safety and confidentiality of patient data at risk. These vulnerabilities range from outdated software and inadequate password practices to deceptive phishing attempts, unprotected mobile devices, and unsecured networks.
Outdated software provides an easy entry point for criminals, making regular updates an essential part of a healthcare provider’s cyber security strategy. Weak passwords are another common vulnerability, with robust password protocols and multi-factor authentication key in fortifying this line of defence.
Phishing scams, often delivered via email, can trick employees into providing sensitive information or granting access to secure systems. Regular employee training can ensure that all staff members are aware of these threats and know how to spot them.
Lastly, if you’re in the healthcare industry, you need to be vigilant about the evolving cyber threats. With sophisticated ransomware attacks targeting medical devices and health credentials, it’s crucial to have proactive risk management and governance strategies in place. By addressing these vulnerabilities, healthcare providers can continue to deliver safe patient care and maintain trust in their ability to protect sensitive health data.
Preventing Cyber Security Breaches in Healthcare
It’s no secret that patient data is highly sought after by cybercriminals. This makes it an absolute priority for healthcare organisations. There are a few essential activities you can do to help stave off interruptions to care delivery and data breaches, these include:
-
- Employ robust governance structures
- Implement risk management strategies
- Use multi-factor authentication
- Conduct regular staff cyber security training
With proactive measures like strong passwords, regular risk audits, and ready-to-implement incident response plan, healthcare providers can secure their IT infrastructure and ensure the safety of patient outcomes.
Strengthen Email Security
Securing electronic communication is vital in the healthcare industry. Emails, in particular, often become the prime target for cyber attacks due to the confidential patient data they often contain.
To protect this communication channel, healthcare providers should employ rigorous security measures. This begins with comprehensive staff training programs, focusing on identifying and responding to malicious emails. It is essential to highlight the risks of phishing attacks, stressing the necessity of double-checking email senders and being cautious with email attachments or suspicious links.
Furthermore, healthcare providers should implement stringent password policies, emphasizing complexity and regular password changes to prevent unauthorised access. Implementing MFA adds another layer of protection, further reducing the likelihood of breaches.
Finally, healthcare organisations should deploy advanced spam filters and secure email gateways. These technology solutions can detect and quarantine potential threats before they reach the inbox, providing an additional safeguard for sensitive patient data.
Phishing Prevention Strategies
We’ve mentioned phishing a few times. And it’s no surprise why. Phishing remains a huge issue for the healthcare sector.
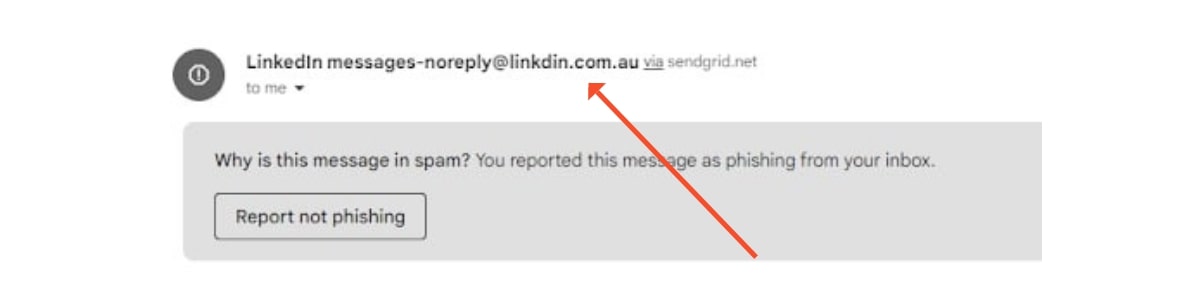
Firstly, continuous staff education is vital. Hold regular training sessions to ensure employees can recognise the signs of a phishing attempt. Red flags include:
-
- Deceptive email addresses
- Urgent language
- Spelling mistakes
- Unexpected email attachments
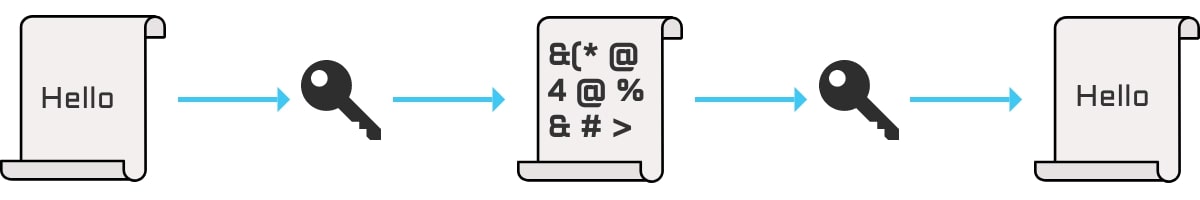
Secondly, implementing technical safeguards such as MFA and data encryption can reduce the potential impact of a phishing attempt. MFA requires additional verification beyond a password, making unauthorised access more challenging. Encryption, on the other hand, ensures that even if data is intercepted, it remains unreadable to unauthorised parties.
Also, healthcare providers should consider using anti-phishing tools and software that can help detect potential emails and quarantine them before they reach users’ inboxes.
Finally, staying up-to-date with current cyber security threats and trends is essential. This way, you can be prepared to neutralise new types of of phishing tactics.
Cyber Security Regulations and Compliance in Healthcare
Healthcare providers need to adhere to strict cyber security regulations. Ensuring compliance with various directives like the Privacy Act 1988, General Data Protection Regulation (GDPR), and Health Insurance Portability and Accountability Act (HIPAA) is a non-negotiable aspect of modern healthcare.
Risk assessments, developing all-inclusive cyber security plans, and offering regular employee training are all critical tools in the fight against cybercrime. As more medical devices are being linked to the Internet of Things (IoT), organisations need to identify and address vulnerabilities promptly. Any breach of security can disrupt healthcare service delivery and have severe implications on patient safety and outcomes.
The Role of HIPAA and the Australian Privacy Act in Cyber Security
Compliance with regulations such as HIPAA or the Australian Privacy Act is a must for all healthcare providers. This involves performing systematic risk assessments, implementing protective measures against cyber threats, and educating the workforce on best practices. Failure to comply with these regulations could result in fines or legal actions, not to mention severe reputational damage.
Telehealth and the Implications for Cyber Security
With the growing popularity of telehealth services, there is an increased need for modern and relevant cyber security guidelines. Protecting the confidentiality and security of electronic health records (EHR) and personal health information (PHI) is paramount. Providers of telehealth services must implement strong encryption protocols and secure login processes, in line with HIPAA and Privacy Act regulations.
Implementing Cyber Security Solutions in Healthcare
The implementation of cyber security solutions in healthcare is not just a matter of protecting data, but of ensuring continuity of patient care and protecting customer trust. With the right approach, healthcare providers can build a resilient defence against cyber threats.
Risk Assessment
Solid cyber security in the healthcare industry begins with a comprehensive risk assessment. By evaluating potential vulnerabilities with hardware, software, medical devices, and data storage practices, you can identify and manage risks.
Defence in Depth
Adopting a multi-layered defence strategy is a crucial step. This approach involves multiple layers of security controls and countermeasures. Through firewall installations, intrusion detection systems, and secure gateways, an all-encompassing defence ensures that threats are stopped early.
Robust Access Control
Access control should sit at the heart of your defence strategy. Implementing MFA, role-based access, and secure passwords can prevent unauthorised access to sensitive patient data. Data access should be granted strictly on a ‘need-to-know’ basis, tailoring the access rights to each employee’s role.
Encryption
Encrypting data both at rest and in transit makes any intercepted data unreadable to unauthorised parties, adding an extra layer of security to your organisation.
Cyber Security Training
A critical part of any cyber security strategy is regular training for all staff members. Most cyber threats exploit human error, so an informed and vigilant team can significantly reduce the risk of a successful cyber attack.
Incident Response Plan
Finally, a strong incident response plan can mean the difference between a quick recovery and a damaging, prolonged ordeal. Such a plan outlines how to respond swiftly and effectively to breach a breach to minimise damage.
Conclusion
Cyber security is an essential aspect of the healthcare sector. It is crucial to protect patient information from cyber threats and ensure compliance with regulatory requirements. Healthcare organisations need to take proactive measures to prevent security breaches and implement robust solutions that can detect and prevent malware attacks. Additionally, regular employee training is vital for maintaining a strong culture of cyber security and adopting best practices in the organisation.
More Like This
Cyber Security Strategy: A Comprehensive Framework
Having a well thought out and correctly implemented Cyber Security Strategy can help businesses avoid a huge amount of damage if they find themselves under attack. Let’s explore the importance of cyber security and how to avoid the sort of security failure that can destroy a company.
Windows 10 End of Life (EOL) and What it Means
Microsoft has announced that October 14, 2025, will be the End of Life (EOL) date for Windows 10. Windows 10 EOL is set to affect all versions of Windows 10, including Home, Pro, Education, and Enterprise. Research from Lansweeper indicates that only 23.1% of...
ISO 27001 Certification in Australia: A Comprehensive Guide
Business data is like a treasure for cyber criminals. In fact, buried in almost every organisation's information assets are details worthy of holding ransom. So, how do you protect it? With ISO 27001 certification. ISO 270001 is more than just a standard industry...